Setting the Pace
Amazon AWS lets a thousand flowers bloom, Microsoft Azure has curb appeal, Google Cloud is the new gold rush. Google Cloud reported Q3 revenues of US$4.99B, an increase of 45% year over year. During the same period, Google Cloud's operating loss has narrowed from US$1.2B to US$644M. Partners are optimistic. Although Google's partner program may be nascent, it is evolving rapidly, setting a frenetic pace and speeding down the right track. The partner management team within a vendor organization is responsible for the quality of partner relationships, a critical responsibility. Ramping up new partners is expensive and time-consuming. Partner portfolios deliver the most significant returns when vendors achieve high buy-in levels and mind share within their partner communities. Partner management isn't defined solely by relationship quality, though. The effectiveness of individual relationships and partner programs and activities can be measured in terms of sales impact – and sales impact itself is generally driven, at least in immediate terms, by the quality of sales enablement and support
Kevin Ichhpurani, Vice President, Global Partner Ecosystem & Business Development at Google, is creating a partner differentiation strategy. The strategy includes a no-services friction partner first approach, developer training, selling to line of business buyers, incentives alignment, and driving marketplace revenue. Carolee Gearhart, Vice President, Global Channel Sales & SMB Sales at Google, takes the strategy further by clearly defining fundamental tenets of partner advantage – simple, collaborative, innovative, and built for growth. Google never built Google Cloud as a channel business. To begin with, Google Cloud is enabling partner transparency, increasing visibility of information, and simplifying lead registration.
Google Cloud has two main product lines: Google Workspace, a subscription SaaS solution, and Google Cloud Platform, a cloud consumption solution. Since they are different products, they have different buyers, buying economics, and competitors. To have an efficient partner program, Google is building a program that meets where the customer is buying rather than changing the sales motion. Instead of creating a partner program for different partner types, Google is developing a program based on engagement models. Early on, Google realized that it does not have an installed base to which partners can sell renewals. Partners, therefore, have to visualize compelling economics to invest in Google Cloud Platform and Google Workspace. Hence, Google has invested in activity-based incentives in the pre-sale stage. Incentives that drive customer demand and lead to sales. Partners have differentiated motivations that drive new customer acquisition, upgrades, and multi-year contracts for Google. It has attractive deployment incentives and recently introduced adoption and consumption incentives, giving partners incremental profitability and incentivizing them to grow their book of business.
Partners are listening
Partners are listening and increasing their resource investments in GCP. Techaisle data shows that 58% of partners are building in-house expertise in Google Cloud. And 62% of SMB-focused partners are either currently offering or planning to offer Google Workspace solutions. We have spoken with many AWS, Azure, and Google Cloud partners in the last six weeks. As one partner put it most eloquently, "…but the reason we are standardizing on GCP is that it offers some of the best incentives that are out there. We used to work with AWS as well. And previously, my last organization worked heavily with AWS and Azure. We knew that Google had one of the best hosted Kubernetes offerings that are out there. Once we started working with Google, we found out that not only were we right, but Google also can manage Kubernetes clusters across all the clouds. And we also wanted to get into a little bit more data analysis and, in some ways, machine learning. Google has its Cloud Vision API, its natural language processing engines, Big Query, and just a mighty engine for any data analysis services. Microsoft, Amazon likes to say that they offer a better ecosystem, but we wouldn't necessarily consider that ecosystem a mature one just yet. There are not as many integrations as they are marketing. And Google has so far stayed true to its word on what they were able to promise as far as just raw processing power."
Thoughtful incentives enabling partner engagement
A key enabler for partner intimacy is the alignment of incentives for the entire customer lifecycle – from demand generation to customer adoption and cloud consumption. Google's attention to detail for both pre-and post-transaction is a vital partner empowerment lever. It naturally has a tremendous revenue flywheel effect for the partner. Google's deep focus on pre-sales incentives for partners has the partners excited. When PoCs make or break customer relationships, pre-sales funding is essential. As another Google partner told us, "Our incentives primarily come in the form of PSF and leads that Google funnels our way. So, during the SOW process, a significant portion of the SOW is paid for by Google. We do a lot of proof of concepts and pilots and just set them in secure landing zones. And I'd say probably say the large majority of PSF probably goes towards those types of engagements."
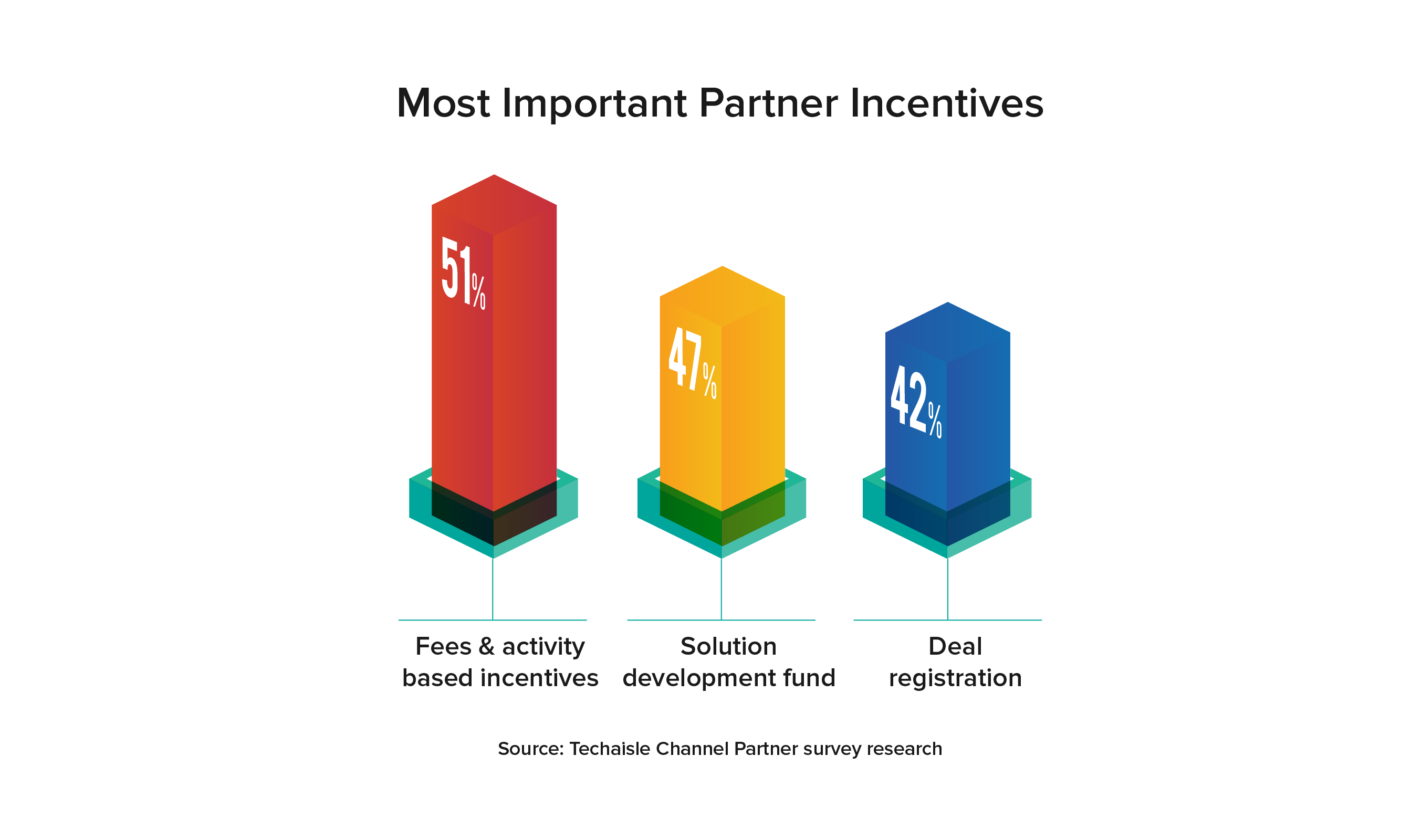
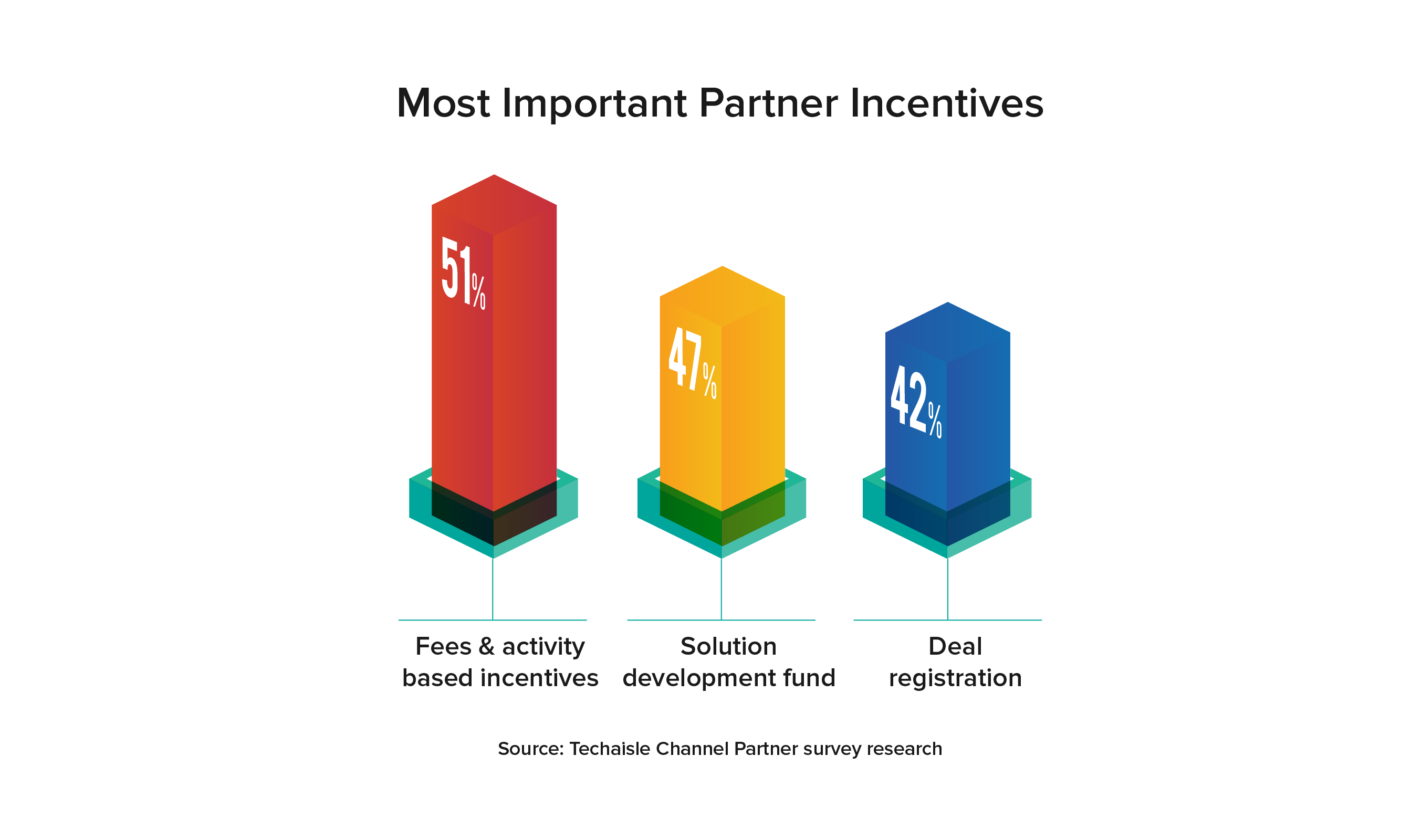
Sales incentives are one of the areas of highest vendor channel investment. Techaisle's partner research shows that fees and activity-based incentives, solution development funds, and deal registration are necessary enablement incentives for 40% to 50% of partners. Over 60% of partners prefer Sell To/Sell With sales models, indicating the need for co-sell, co-marketing, and IP-led solutions. Data shows that 29% of partner revenue is coming from IP-led solutions. The steady rise in demand for solution development funds and the decline of market development funds shows that partner IP-led solutions are becoming front and center. Recognizing the trend, Google has devised incentive programs to engage with different partner business models and partners selling Google Workspace and Google Cloud solutions.