As an analyst who has followed Zoho for many years, interacting with their partners and extensive customer base, I have tracked Zoho’s steady evolution from a collection of apps to a true platform. With its November 2025 release, Zoho is making its most profound market statement yet. This is not just a product update; it represents a fundamental strategic shift from selling a software suite to delivering a unified business operating system.
For years, the market has compelled organizations to assemble a constellation of "best-of-breed" applications, resulting in a fragmented, costly mess that Zoho aptly calls the integration Frankenstein problem. This release is Zoho's definitive answer, designed to replace that complexity with a new core value proposition: operational peace of mind.
The Strategic Bridge: A Logical Chain to Value
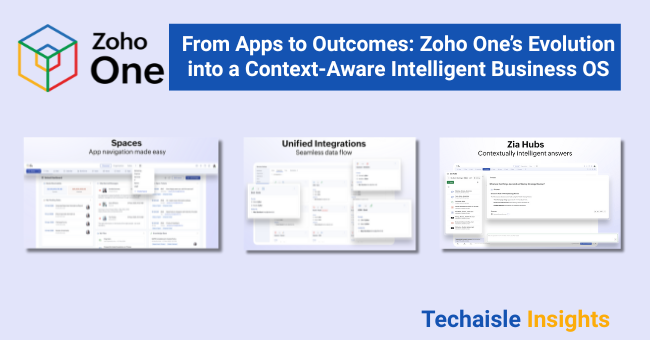
The three pillars of this release—Experience, Integrations, and Intelligence—are not separate features; they are interdependent. They are a single, logical chain of cause and effect that forms Zoho's entire value proposition. This strategic unification arrives at a critical moment, as businesses seek to harness the power of AI and move beyond the fragmented, app-centric model of the past. This chain is built as follows:
- The Unified Experience is the Promise. It serves as the core promise to the user: a simple, coherent OS where all business functions are in one place
- The Deep Integration is the Technical Enabler. It makes the promise possible, providing the essential, native plumbing that allows 50+ applications to act as one.
- The Unified Intelligence is the Ultimate Payoff. Because the experience and data are unified, Zoho can deliver on the true goal of AI: intelligence that is powerful because it is both holistic and contextual.
The Pillars of Unification














