The SMB and midmarket are not just adopting new tools; they are signaling a fundamental shift in how they want to consume security. The convergence of massive demand for AI-driven automation, soaring MDR adoption, and rapidly growing Zero Trust awareness is creating a new market for an "Autonomous SOC" that delivers intelligent, expert-level security as a service.
The Coming of the Autonomous SOC: A New Security Paradigm for SMBs and Midmarket
For decades, the Security Operations Center (SOC) has been the exclusive domain of large enterprises with deep pockets and extensive in-house expertise. Our latest Techaisle data reveals that this paradigm is about to be shattered. A powerful convergence of three trends—the desperate need for AI, the meteoric rise of Managed Detection & Response (MDR), and the strategic embrace of Zero Trust—is paving the way for the "Autonomous SOC," delivering sophisticated security outcomes as a utility for the SMB and midmarket.
This is not speculation; it is a direct response to the market's most pressing challenges. The number one security challenge for businesses of all sizes is staffing. Businesses simply cannot hire their way out of the complexity and volume of modern cyber threats. They are turning to technology and new service models for the answer.
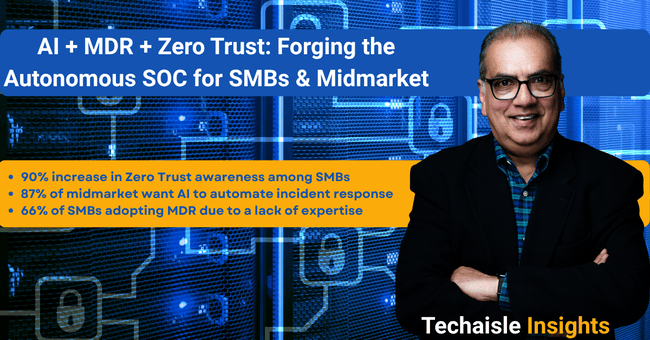
The Three Pillars of the Autonomous SOC