Techaisle Analyst Insights
The growing importance of IT and Security to SMB business
It is evident from even a casual tour of a modern SMB office that IT has become integral to business activities. Email and communications systems that meld conventional, web-based and mobile phones; and social collaboration tools on the web and within offices provide the basis for connections between companies and customers, across processes and with suppliers, and between staff members. Productivity applications like spreadsheets, graphic presentation packages and word processors enable users to complete tasks, while enterprise applications capture and report on financial data and organize processes.
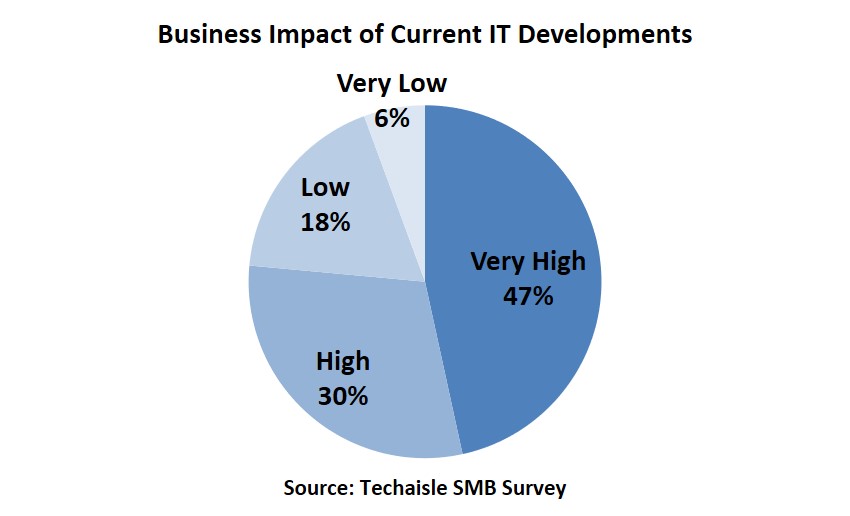
Given the nearly-ubiquitous nature of IT, it is fair to wonder: are we “there” yet? Have all of the technologies that one needs been deployed? Results from a recent Techaisle survey of 1455 North American SMB IT managers (ITDMs) and business decision makers (BDMs) conducted by Techaisle indicate that there is still a voracious appetite for new IT-based business solutions. Asked to evaluate the business importance of current IT developments, 77 percent of SMB survey respondents reported that new IT systems would have a very high to high impact to their organizations. Only 6 percent believe that new IT products and services will have little impact on their businesses. Clearly, SMB BDMs and ITDMs agree that new technology will play an important role in making their businesses more profitable, and their employees more productive.
SMB IT is pervasive – and becoming more so but security needs to be the focus
The evidence of IT’s ubiquitous presence is not limited to the anecdotal evidence found in a review of SMB office activity – it is also seen in the financial allocations of public and private-sector organizations. It isn’t an exaggeration to state that in today’s business world, IT infrastructure is business critical infrastructure. SMBs are heavily invested in IT, with IT-dependent processes throughout their operations.
This ubiquitous dependence on technology means that systems failure will reverberate throughout all of a company’s daily operations. There is no way to disaster-proof against IT failure with insurance; appropriate investment in IT security processes, technologies and management strategies is the only way to capitalize on the productivity benefits of IT without creating exposure to organizational paralysis in the event of a malware invasion, a hacker attack or an employee’s negligence or malfeasance.
SMBs that invest in building responsive and capable IT security infrastructure and practices are able to move more quickly and surely than their competitors to adopt new technologies in new areas.
A sound argument can be made that because of cloud computing, the capacity for rapid technology adoption is more important today than ever before. With cloud, the cost of developing and marketing new applications has dropped by at least 1-2 orders of magnitude – and with that reduction in cost has come a proliferation of new applications. These new offerings enable automation in areas that previously could not be addressed, because the cost was too high and/or because the market was too diffused or ill-defined.
Today, though, it is possible to acquire solutions that address any combination of IT, back-office and customer-facing tasks. SMBs that can adopt these applications and orchestrate across them, tying them into a coherent IT/business architecture, can gain new capabilities, improve process efficiencies and/or reduce costs much faster than their competitors.
However, each new application creates a need to secure users, data, and the environment that the solution integrates into. This conjunction of opportunity and exposure illustrates the connection between business success and effective IT security: firms that build robust frameworks can capitalize on the opportunities, while those that treat security as an onerous requirement that is invoked each time a new system is contemplated will be slow to adopt – and profit from – new IT-enabled business process efficiencies.
Patchwork solutions that combine products from multiple vendors inevitably lead to the blame game with the antivirus company pointing a finger at the firewall company, who points the finger at the identity management vendor. Each of them is responsible for only part of the problem. It’s not a system. It’s not efficient. And it’s not very secure.
Clearly IT is important to business success, however, the link between security and business success is less transparent, but it is evident nonetheless. If security is viewed as an “anchor”, management will be constrained in capitalizing on IT-enabled business system potential by a governance framework that is too slow and unwieldy to keep pace with emerging opportunities. While there is upside and downside from a business/security perspective, security is an enabler of business success and profitability.
Upside:
- IT matters to SMB business success
- SMBs are investing heavily in IT
- IT will continue to increase in importance
- IT is business-critical infrastructure
Downside:
- Interruptions in IT service will be felt clearly and immediately
- There is no real way to disaster-proof
- The impact of failure has expanded tremendously
Bottomline: IT matters to business success, and security matters to IT success. IT security has the potential to become a high-value, strategic activity, rather than an "anchor" or cost of doing business.
When you subscribe to the blog, we will send you an e-mail when there are new updates on the site so you wouldn't miss them.











