Techaisle Analyst Insights
SMB IT is challenged and its role in supporting governance-risk-compliance
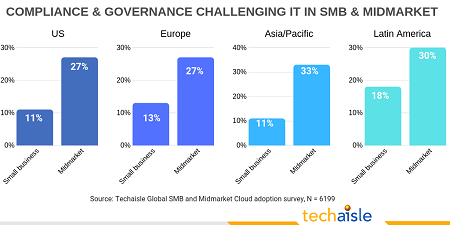
Managing governance, risk and compliance is an IT challenge for over 1/4th of midmarket firms and slightly more than 1/10th of small businesses in each geo – US, Europe, Asia/Pacific, Latin America. See chart below. In an SMB context, “governance” is at least somewhat analogous to “taste” in home décor, or “sustainability” in supply chain practices: easy to acknowledge as important, but difficult to define. What is easy to delineate is the notion that governance has important linkages to issues that are of vital importance to SMB management:
- risk mitigation,
- regulatory compliance, and
- protection of the corporate reputation.
Governance is a way of describing the objectives of senior executives, or of the company as a whole; it is the approach that determines how the SMB interacts with its customers, its suppliers, and its community. Oftentimes, the term ‘governance’ is coopted by IT professionals, who talk about issues like “IT governance,” “cloud governance,” or “data governance.” These are important concepts, but they really refer to policies and controls.
Policy is the ‘glue’ that connects governance and security: SMBs benefit from thinking about management issues first, and then developing positions that guide security decisions. This works as a starting point for an SMB security strategy. However, there are challenges that arise from specific IT usage patterns or events that impact an SMB’s risk profile.
Consider the issues cited in the chart below - examples of usage patterns that affect an organization’s security stance: use of cloud, and ‘shadow IT,’ or user-managed applications and/or storage that may not align with corporate security policies. It’s possible to simply state that any use of cloud or user-managed IT services needs to adhere to these policies, but the reality is that they may not: for example, a cloud supplier’s SLAs may not include corporately-approved escalation processes, and users may lack understanding of (or concern for) corporate IT guidance. This doesn’t mean that use of cloud and shadow IT should be banned – cloud is an important IT service delivery option, and to some extent, shadow IT reflects innovation within the business.

What it does mean is that security technologies and processes have to be able to cover issues like cloud and shadow IT in ways that align with corporate governance policies. Similarly, attacks from hackers or exfiltration of corporate data caused by lost laptops or smartphones (or via malicious employees) often aren’t covered by specific governance policies within an SMB, but these kinds of events represent risk that most SMB executives would consider to be unacceptable. Here, too, the staff member (or supplier) responsible for IT security needs to be sure that the technologies and processes that have been put in place will provide the level of protection needed to adhere to corporate governance policies.

SMB executives should work with their technical teams to arrive at an assessment that looks at a supplier through both technical and management lenses. The combined business/IT perspective can consider whether the supplier is likely to act as a partner to the business: whether it is trustworthy, whether communications will be regular and effective, whether the relationship will stay viable over time. In the end, these issues determine whether and how a supplier meets the overarching requirement: providing the security layer needed to support the SMB’s governance objectives.
To read more on how IT can help SMB create a process and workflow for managing governance, compliance and risk download the white paper.
When you subscribe to the blog, we will send you an e-mail when there are new updates on the site so you wouldn't miss them.











