Techaisle Analyst Insights
IBM – motivating midmarket firms to think strategically about cloud security
A blog “Big Data in the Cloud - an ideal solution for SMB banks” that we wrote touched a nerve, in a good way. Post blog, in our several discussions with both large and community banks we find that cloud objection is largely based on the size of the bank. In addition, regulatory compliance concerns are huge as most midmarket businesses and banks in particular spend a lot of money being compliant. With the move to cloud they want to make sure that the investment extends to the cloud without being exposed to security breaches and from a regulatory point of view.
What is clear is that migration to cloud is forcing businesses to think differently about security, in very standardized ways because the delivery of cloud service is standardized. It is also pushing them to automate security because utilization of cloud is dynamic, elastic, automated and fluid thus making manual or even semi-automated security processes unmanageable. However, this approach creates multiple vulnerabilities. The bad guys themselves are taking advantage of all the cloud technologies and are becoming a lot faster and more automated than the businesses. Security therefore becomes a moving target and cloud security is a perfect opportunity for businesses to improve defenses and reduce risks.
While most midmarket businesses are reactive, hunting after point solutions when something goes wrong, others are taking a proactive approach to risk and threat so that they have more fluidity in the way they respond when a threat occurs.
IBM security is on a path to help businesses think differently about cloud security. It is moving the businesses along a maturity curve from reactive to proactive to optimized. Optimization refers to the difference between being able to weather an attack and continue with business and how much time could one can shave off and how much cost could be optimized for being able to respond to that event in reducing risk.
As Sharon Hagi, Global Strategist and Senior Offering Manager, IBM Security, said in an interview “the state that IBM is advocating goes beyond reactive or proactive. We call it the optimized state where organizations use automation coupled with predictive security analytics to drive towards a higher level of efficiency. By mixing the elements of proactive approach, automation and security intelligence businesses can actually get to the point where they are a lot more efficient and they actually reduce time and cost to respond to risk.”
IBM is differentiating and trying to distance itself from others in a number of different ways. IBM has a managed security services practice with ten plus security operation centers around the world servicing 133 different countries with 6,000 security professionals and its research lab X-Force provides actionable threat intelligence and insights for business and IT leaders. IBM monitors 10,000 security customers globally, 70 million end-points with 20 billion events per day, has made enormous investments in security intelligence analytics platform that allows it to distill information, identify threats and respond quickly.
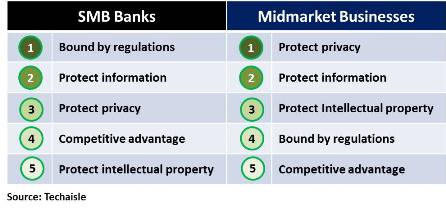
But for banks and businesses that come under deep regulatory scrutiny, security goes beyond managed services and is a major psychological barrier to cloud adoption triggering a high level of fear-factor. Recently, we posed a fundamental question of “Why do you want security” to banks and midmarket businesses in general. The responses received could easily be bucketed into five categories:
And this is the environment that IBM is trying to address. It is an uphill task of education, evangelism and prodding businesses to think differently. IBM’s Sharon Hagi is looking at the entire migration to cloud as supply chain risk management issue where businesses need to manage not only their in-house risk but also third party and supplier risks. IBM’s security managed services is positioning its value in monitoring both its own platform as well as monitoring and managing risk in Amazon, Azure, Google and just about everywhere businesses are going for their hybrid or multi-cloud implementations. Sharon Hagi, says, “We need to manage risk everywhere with analytics and intelligence and integrated solutions that work not just in our cloud but in all clouds.”
Amberoon, an IBM partner which provides Big Data solutions for banks, chose IBM SoftLayer for its implementation because the underlying infrastructure had been independently audited to be compliant with FFIEC requirements and industry best practices for financial services.
“Financial institutions represent the gold-standard for security,” said Shirish Netke, CEO at Amberoon. “The reliability of the IBM Cloud under the hood is a critical factor in building confidence with our customers”.
Skyhigh Networks, which is a Cloud Access and Security Broker (CASB) and another partner of IBM, works on discovery and risk assessments of scale and scope of security problems within a business to address problems of shadow IT and unsanctioned, ungoverned use of product applications.
Skyhigh Networks is especially bullish on IBM. Kamal Shah, VP of Product and Marketing said, “as the use of cloud has exploded, Skyhigh has experienced tremendous success with customers who need to manage risk from shadow IT and securely enable sanctioned IT – all from a single cloud security platform. Due to IBM’s security leadership, we sought early on to partner with IBM which offers managed security services around Skyhigh solutions. In the Financial Services sector, a market where IBM has a significant customer base, Salesforce and Box are examples where data going to these services needs to be compliant with strict internal policies and external regulatory requirements. SMBs and midmarket firms are no different. They use Salesforce, Office 365, and other cloud services and need to make sure they are using those services securely and complying with regulations. SMBs tend to rely on managed services partners more than enterprises to improve IT security and as a way to keep IT costs under control. They need a partner like IBM who can research, recommend, deploy, and operate the latest in cloud security solutions".
IBM SoftLayer is compliant with major industry and regulatory commercial workloads, such as PCI, HIPAA, FDA, GxP, and European Commission. All IBM SoftLayer data centers are managed to SoftLayer security policies, based on NIST 800-53 framework, are audited to SOC2 Trust Security Principles as evaluated in the third party SOC2 Type II assessment. In addition IBM SoftLayer provides VLAN configurations on bare-metal servers. Further its compliance and operations are ISO 27001 certified and vulnerability assessments can be done based on OWASP guidelines.
However, one of the most important tenets of IBM security is its triple-layer network security (a segmented triple layer network topology with a public network, a management network and a private network), which no other cloud provider has. And because IBM has a triple-layer network security architecture, it can disable public ports on the database server and the customer can go to the application, the application can talk to the database, to the private network, thus providing an extra layer of security. IBM uses CASB technologies to help businesses govern and protect access to cloud applications.
Another frequent question that comes up in discussions with midmarket businesses revolves around encryption of data at rest and in motion. IBM has a solution through its IBM Cloud Data Encryption Services which is a data-centric solution providing a homogeneous way to protect and control access to all data, whether at rest or in motion across heterogeneous systems.
Nevertheless, in Techaisle’s discussions with midmarket businesses we find that extending the protection bubble is not an easy conversation. Businesses must be open to have an open-minded discussion that goes beyond technical capabilities. They have to first fundamentally realize the need for a strategic approach to security. Most businesses are trained to do a “bake-off” of capabilities across providers and therefore miss a perfect opportunity for a comprehensive review of safeguarding their businesses from a constantly fast moving target. Things in the cloud do not happen week to week. Things in the cloud get deployed in minutes. Things change even by the second. Businesses should begin by asking themselves:
- Do they have the right people in the organization who have the right skills to manage new technologies?
- Do they have the right processes?
- Do they have security policies matching the cloud environment?
- How do they elevate C-level attention to needing to move to a proactive posture?
Attacks on data resources will continue to increase, the threats will continue to proliferate, with new threat types emerging every day; and with the expanding reliance on cloud IT, security failures will be increasingly visible and damaging. Nevertheless, the “needle” is definitely trending upward for IT security. The security vendors continue to improve the breadth, capabilities and integration of their products and complement them with advanced services. IT security managers themselves are increasingly able to move past firewall configuration and malware deployment to addressing issues at the core of business processes.
In an environment where security is a strategic business issue, IBM is positioning itself at the cusp of cloud security transformation. Standardization of protection is not necessarily a bad thing. If it works to reduce risk for the majority, then it is good progress. SMBs and midmarket businesses do need to think differently and more innovatively and strategically about security going forward.
When you subscribe to the blog, we will send you an e-mail when there are new updates on the site so you wouldn't miss them.











