Techaisle Analyst Insights
The End of the Cybersecurity "Find It" Era: How Palo Alto Networks Is Betting on "Fix It"
The enterprise honeymoon with Generative AI is officially over. For the past two years, organizations have been enthralled by “AI that talks” - chatbots that summarize documents, draft emails, and write basic code. But the market is now aggressively pivoting to a far more volatile phase: “AI that acts.” We are entering the era of Agentic AI, where autonomous agents execute complex, multi-step workflows across applications without human intervention.
This transition fundamentally breaks legacy cybersecurity architectures. In a set of deeply consequential announcements at RSAC 2026, Palo Alto Networks has not just released new products; it is laying the groundwork for a significant acceleration of platform consolidation across the security vendor ecosystem. Through the launch of Prisma AIRS 3.0, Prisma Browser with Agentic Browsing capabilities, Prisma Browser for Business, Prisma SASE, and Next-Generation Trust Security (NGTS), PANW is forcing a market reality: the days of merely finding vulnerabilities are ending. The industry is shifting to an automated, platform-driven “fix it” mandate. For technology vendors, channel partners, and enterprise buyers, understanding this shift is the difference between capturing the next decade of margin and falling into irrelevance.
The 1% Problem
Generative AI, in its current mass-market form, solves the “90% use case” - generalized productivity where a hallucination is an acceptable margin of error. Cybersecurity does not have that luxury. It is a 1% problem, requiring absolute precision where a single edge-case failure can result in a catastrophic breach. As Nikesh Arora, Chairman and CEO of Palo Alto Networks, put it, “you wouldn’t let an untrained LLM drive a car on a busy street - it took Waymo billions of dollars and 15 years of specialized training before society trusted it to drive unsupervised - and you cannot trust a generalized LLM to autonomously remediate enterprise network infrastructure.” Cybersecurity demands the same degree of precision, built on proprietary algorithms and massive volumes of proprietary threat data, not general-purpose reasoning.

This is the fault line that will trigger the next wave of consolidation. The market is flooded with posture management startups that scan environments and throw alerts onto dashboards - the “find it” model. But when enterprise architectures are saturated with autonomous agents executing at machine speed, humans cannot manually triage alerts. The enterprise requires platforms that provide aggregate context - across network, endpoint, identity, and application - to safely authorize autonomous remediation.
The logic is unforgiving: if an autonomous security agent misinterprets an alert and decides to reboot a core router to isolate a perceived threat, it could take down the entire business. This is why Techaisle believes the next era of cybersecurity will be defined by what we term "Context Custodians" - platforms possessing the deep architectural understanding of network flows, identity graphs, application dependencies, and data lineage required to safely authorize autonomous remediation. Only Context Custodians can transition from finding a problem to confidently fixing it. Point solutions that lack this comprehensive cross-domain context will be increasingly subsumed.
Set against the competitive field: CrowdStrike has formidable endpoint telemetry but lacks a network-native control plane for agentic enforcement. Zscaler owns cloud-delivered security but has not articulated an agentic identity story. Wiz (now part of Google Cloud) is the canonical “find it” player - brilliant at discovery, lacking in autonomous remediation. Newer agentic-AI security startups tackle narrow slices without cross-domain context. PANW’s differentiator is the convergence of network enforcement, browser-level visibility, AI runtime controls, endpoint agent monitoring (via the pending Koi acquisition), and machine identity governance (via CyberArk) into a single control and action plane. No other vendor currently ships across all five vectors.
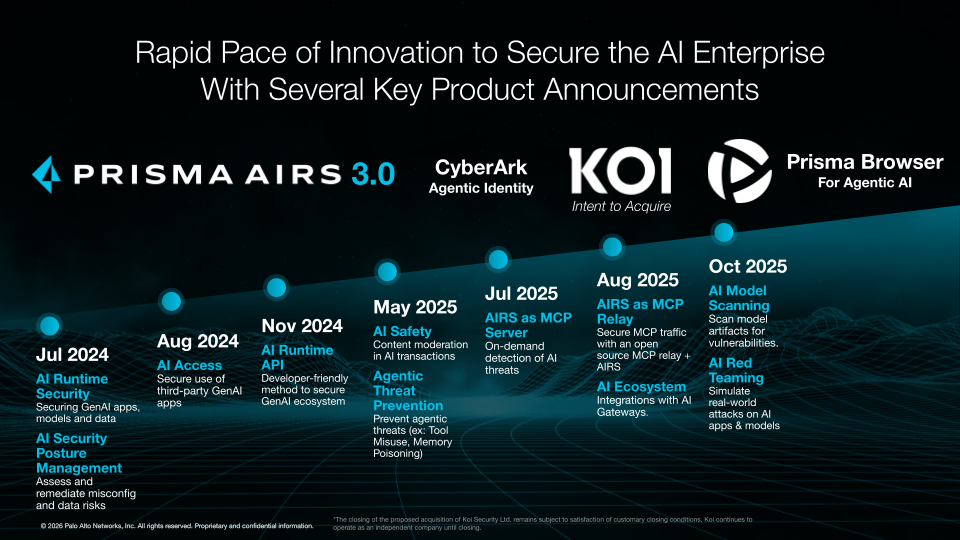
Prisma AIRS 3.0: Taming Agentic Sprawl
The most immediate crisis facing security leaders is “Agentic Sprawl.” Nearly every major SaaS application - from Salesforce to Workday to ServiceNow - is embedding agents that access corporate data. Developers are simultaneously building proprietary agents on platforms such as Azure AI Foundry, Agentforce, and Google Agentspace, while employees are independently deploying coding agents such as Claude Code and Cursor on their local machines. The result is a completely unregulated supply chain of skills, hooks, MCP servers, and autonomous code - with no centralized registry, no credential governance, and no mechanism to even count how many agents are operating inside the enterprise perimeter.
Prisma AIRS 3.0 shifts from securing static AI applications to securing the dynamic agent lifecycle across three critical vectors.
- Shift-left supply chain defense: Before deployment, AIRS scans agent artifacts - code, MCP server configurations, skill definitions, hook integrations - and runs behavioral red-teaming, simulating context-aware attacks to find exploitable vulnerabilities. The agentic supply chain is currently a chaotic, unregulated marketplace of third-party skills and open-source hooks. If a malicious hook is embedded pre-deployment, the agent effectively becomes an authorized insider threat. For channel partners, this necessitates a shift from reactive alerting toward pre-deployment auditing and continuous agentic governance as a high-margin recurring service.
- The Agentic Gateway: Traditional AI firewalls operating at 100-500ms latency choke multi-agent workflows where a single task might require 50 micro-handoffs between agents, tools, and skills. PANW is building an AI Agent Gateway using deterministic detectors that process structured tool calls and JSON payloads at significantly reduced latency, leveraging the inherent structure of agentic communications rather than running every input through broad ML classifiers. Security can no longer afford to be the bottleneck for AI execution. Vendors that cannot inspect agentic transactions at machine speed will be fundamentally engineered out of the modern enterprise stack.
- Agentic Identity: By integrating CyberArk capabilities, PANW bridges human and machine identities, ensuring agents requesting high-risk actions have authorized context. Non-human identities are now proliferating significantly faster than human ones, creating a massive perimeter blind spot. This integration signals the aggressive merging of Identity and Access Management with AI security operations - MSPs must expand their identity practices to govern machine-to-machine interactions or lose control of their clients’ security architectures.
A critical question business buyers must internalize is where the boundary falls between security problems and business logic problems. The answer hinges on context. If the agent’s instructions and tool permissions encode that constraint, Prisma AIRS can deterministically detect and block the violation. But if the business never specified the rule, the failure is an AI accuracy problem, not a security problem. Prisma AIRS extends well beyond runtime enforcement, encompassing model security, automated red teaming, and comprehensive AI posture management. However, for the specific question of security versus business logic, AIRS is a policy enforcement engine for well-defined security rules - not a universal safety net for poor agent design. Enterprises must invest in defining agentic governance frameworks before AIRS can protect them.
The Browser Plays: Enterprise and SMB
For enterprises, Prisma Browser becomes an “AI Launchpad” that decouples the browser from any single LLM vendor. Organizations can bring OpenAI, Gemini, Claude, or others into a secure workspace. The AI Launchpad enables free-form chat conversations with full browser context – including open tabs and browsing history – and provides agentic browsing capabilities for inline actions, such as automatically filling out forms or executing multi-step browser-based tasks on the user's behalf. This is delivered with embedded Prisma AIRS protection, enforcing prompt-injection detection, DLP, and topic guardrails for every AI interaction. This is a direct competitive response to the emerging browser/LLM vendor lock-in trend, where each major AI provider ships its own browser (Operator with ChatGPT, Chrome with Gemini, etc.) and forces enterprises into closed ecosystems. By decoupling the browser from the LLM, PANW positions Prisma Browser as a neutral, secure orchestration layer. Crucially, the browser distinguishes between human and AI actions within the same session, enabling differentiated security policies and comprehensive audit trails - a capability that becomes essential as global AI regulations increasingly demand accountability for autonomous actions taken within enterprise environments.
For the SMB segment, Prisma Browser for Business takes a different approach. At roughly $99 per user annually, it shifts security enforcement directly to the browser runtime, bypassing the network-decryption overhead that makes traditional SASE prohibitively complex for small businesses. The browser sees data post-decryption and pre-encryption, providing native visibility into shadow AI usage and prompt-injection attacks without traditional middleboxes. With 95% of SMB security incidents originating in the browser and the average small business running 36 browser-based applications (50+ SaaS applications for an average SMB), the attack surface is enormous - and growing as employees rapidly adopt AI tools without IT oversight. For MSPs, this changes SMB customer acquisition economics from high-touch hardware deployments to frictionless product-led growth. The strategic question is whether the $99 price point is a standalone profit center or a land-and-expand wedge into PANW’s broader portfolio - the answer almost certainly is the latter, which means MSPs must layer meaningful services - managed DLP policies, AI usage governance, compliance reporting - on top or risk being disintermediated by PANW’s direct channel.
Prisma SASE: Securing the Era of Agentic AI
The browser announcements are part of a broader, more architecturally significant play: the next evolution of Prisma SASE, now purpose-built for the era of Agentic AI. This matters because legacy SASE solutions were designed for a world where every action on the network originated from a human user. That assumption is collapsing. As autonomous agents proliferate across enterprise environments, traditional SASE architectures have no mechanism to distinguish between a legitimate employee action and one initiated by an AI agent – creating dangerous blind spots, including agent hijacking and uncontrolled AI data sprawl.
PANW’s approach is to transform Prisma Browser into a secure AI workspace that serves as the enforcement point for intent validation – assessing the intent of every identity, whether human or machine, and blocking unauthorized actions in real time. This is then unified with AI-lifecycle data protection and autonomous operations to create an end-to-end SASE fabric where machine-speed productivity is matched by machine-speed security. From a Techaisle perspective, this is the architectural connective tissue that ties the browser-level announcements back into the broader network security story. PANW is essentially arguing that SASE must evolve from securing human-to-application traffic to securing agent-to-application and agent-to-agent traffic – and that the browser is the natural enforcement surface for this transition. For enterprises evaluating SASE vendors, the critical question is no longer just throughput and policy granularity; it is whether the platform can natively understand and govern agentic intent at the edge.
The Cryptographic Reset
The quieter but potentially more destructive crisis is the collapse of digital trust. Certificate lifespans are compressing from years to weeks – dropping to 200 days recently, and heading to a mandatory 47-day cycle by 2029. An enterprise managing 5,000 certificates at 47-day intervals faces over 100 renewals daily. Miss one on a VPN gateway or load balancer, and the business goes offline.
Here is the connection most coverage will miss: every AI agent communicating over the network relies on certificates for authentication and encrypted transport. As agents scale from dozens to thousands, the certificate management burden scales in lockstep. The 47-day cycle applied to agentic sprawl is not a 12x operational increase – it is potentially 100x when combined with the explosion of non-human identities. PANW’s NGTS platform, integrating the former Venafi CLM via CyberArk into Strata Cloud Manager, activates existing firewalls as cryptographic sensors, automatically discovering shadow certificates and remediating them before outages occur. For organizations migrating to post-quantum cryptography, cipher-translation proxies bridge legacy protocols to quantum-safe standards without ripping and replacing infrastructure. And in January 2026, PANW launched Cryptographic Inventory and Remediation capabilities as a new product offering – the Quantum-safe Security platform on Strata Cloud Manager – bringing comprehensive visibility to encryption across enterprise-wide assets’ sessions and certificates. For channel partners, the 47-day mandate represents a forced march that creates incredibly sticky managed-service revenue – clients cannot handle the volume manually, and the consequences of failure are immediate business outages.
The Bottom Line
In the agentic era, security must be as autonomous, fast, and decisive as the AI it controls. Palo Alto Networks has articulated a comprehensive strategic vision for agentic security in the market - spanning agent lifecycle management, browser-level enforcement, machine identity, cryptographic automation, and endpoint agent security.
The open question is execution velocity. The AI Agent Gateway is in limited preview, not GA. The Koi acquisition has not closed. CyberArk NHI integration for agentic workflows is still maturing. The strategic direction is correct, but buyers should plan in phases: deploy Prisma AIRS for agent discovery and artifact scanning now, pilot the gateway as it reaches GA, and layer endpoint and identity capabilities as integrations mature. Most importantly, recognize that no security platform will compensate for poor agent governance - define your agentic policies before expecting any tool to enforce them.
The company that stitches together all five vectors first - network, browser, AI runtime, endpoint, and identity - will own the security platform of the agentic era. Based on what I have seen, PANW has a strong hand. But the cards have not all been played.
When you subscribe to the blog, we will send you an e-mail when there are new updates on the site so you wouldn't miss them.











